Key Insights from the 2022 Verizon Data Breach Investigations Report
Released earlier this year, the 2022 Verizon Data Breach Investigations Report (DBIR) collected and analyzed 914,547 incidents, 234,638 breaches, and 8.9 TBs of cybersecurity data. This is the 15th annual report, which was first published in 2008 (the same year the first iPhone was released, for context).
As technology has changed drastically since that first report 15 years ago, our cyber exposure has too. While the amount of data and contributors to this report has grown significantly, the struggle to keep businesses and organizations safe from cyber threats has not.
This report gives security experts around the world better insights into the cybersecurity trends and patterns taking shape across all industries.
To help you get through this 107-page report a little faster, we’ve summed up the key takeaways that IT personnel and business leaders should know:
- Ransomware continued its uphill trend with an almost 13% increase. For context, this is as big as the last 5 years combined.
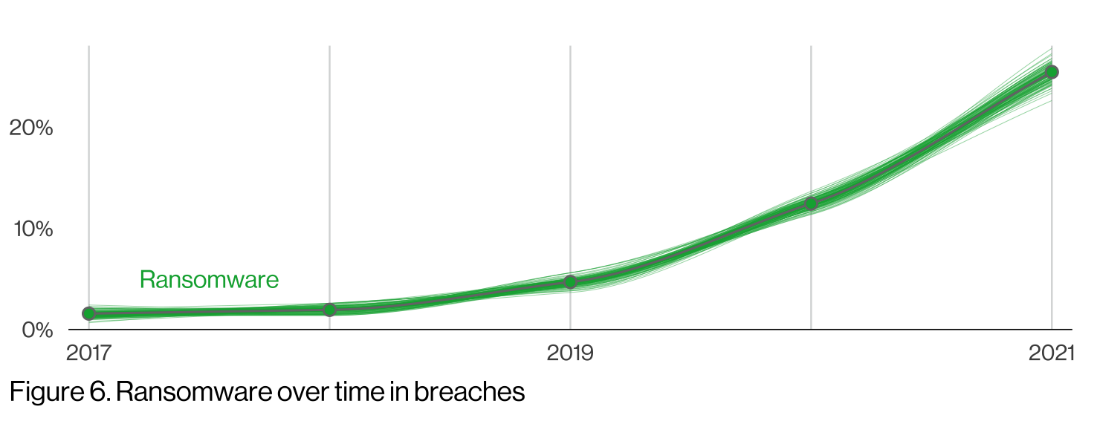
System intrusion, which uses malware or hacking devices like ransomware, was a top pattern and 98% of these incidents were carried out by external parties. Ransomware operators don’t need to look for data of a specific value, they simply need to interrupt an organization’s critical functions by encrypting their data which can provide a substantially higher value, making this tactic enticing.
40% of ransomware incidents involved the use of desktop sharing software and 35% involved email. These are mostly accessed using stolen credentials and phishing tactics.
- Human error has decreased and leveled out from a spike in 2019, but this vulnerability should continue to be a concern as 82% of breaches involved some type of human element.
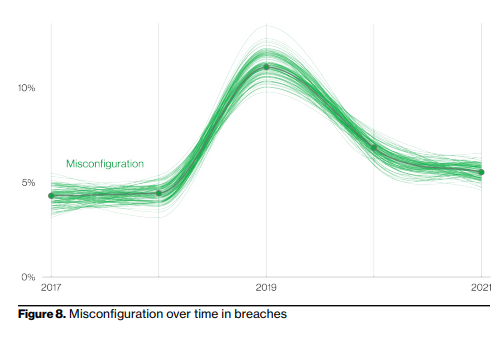
The human element could involve the use of stolen credentials, phishing (which dominates this category), misuse, or a simple error. While only 2.9% of employees actually click on phishing emails, this is still more than enough due to the sheer volume of phishing emails sent every day.
Within this report’s breach data alone, there were 1,154,259,736 personal records breached. If we assumed those were mostly email accounts, that 2.9% of employees that clicked on a phishing attack would equate to more than 33 million accounts phished.
- Despite previous concerns, insider incidents aren’t as common as many think as 80% of incidents come from outside of the organization.
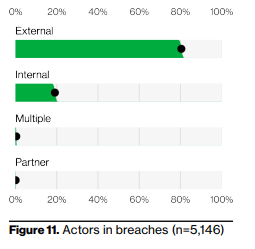
However, the median size of records compromised in an insider breach is nearly 10x the amount of an external breach. While an insider breach is not as common, they can do more damage.
- While payment information used to be the main target of malicious actors, today the data they’re seeking is largely personal information and credentials, which can be more valuable.
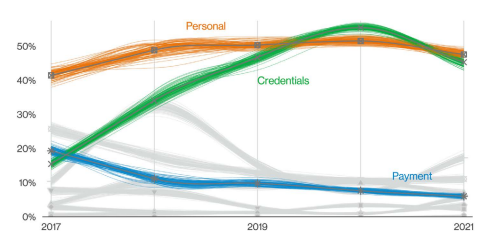
This type of data is useful for financial fraud, there’s a large market for its resale, and it allows criminal actors to masquerade as legitimate users within the system.
- While cybercrime against large organizations makes the news, small organizations are just as enticing to criminals, if not more so. Ransomware and the use of stolen credentials are the most used forms of attack against small businesses.
While many small business owners may assume they’re not a target, that’s no longer the case. Cybercriminals know that small businesses don’t have the IT resources and budget that large enterprises have. While we hear about these large attacks on the news, the average malicious actor is aiming for the low-hanging fruit that is small business.
Next Steps: The Right Security Tactics Will Reduce Your Cyber Exposure
A large hurdle many businesses face is their lack of IT resources and knowledge. While most employees regularly work from a desktop, not everyone is well versed in technology, and most don’t understand functions that go beyond their everyday needs and tasks. This means it can be hard to identify when something is going wrong with your tech.
The DBIR report had a simple and effective way of identifying cyber-attacks: “Think of your computer like a car – if it suddenly won’t start, runs slower, or makes a weird noise, it’s time to have an expert take a look.”
While the unfortunate statistics around cybercrime show that businesses shouldn’t be letting their guard down anytime soon, there are effective ways to protect your organization.
For ransomware, there are four key pathways that threats take that lead to your data estate. Protecting these key pathways can effectively block these attacks from getting through:
Credentials
- Use 2FA
- Do not reuse or share passwords
- Use a password keeper/generator app
Phishing
- Do not click on anything in an unsolicited email or text message
- Set up a method for verifying unusual requests for data or payments
Exploiting vulnerabilities
- Ensure you install software updates promptly so any vulnerabilities can be patched
- Maintain a consistent backup schedule, which should include offline backups
Botnets
- Use antivirus software for all devices
- Ensure that the built-in firewall is switched to “on” for user devices as this may not be the default
In general, there are a few positive trends noted within the industry. Overall, we’re patching more and we’re patching faster. This allows businesses to close and protect potential vulnerabilities before malicious actors can exploit them.
We’re also getting better at detecting and reporting phishing. More people can accurately identify a phishing attempt and are NOT clicking on unusual, suspicious, or unsolicited emails.
We’ve reached the era of cybersecurity in which facing the reality of the cyber landscape we’re all facing is key. A proactive cyber security practice that recognizes your very real risk will help you take steps that can make a true difference in your exposure.
To learn more about achieving a proactive security practice, contact one of our Arraya Cyber Team experts today to start a conversation.
Visit https://www.arrayasolutions.com//contact-us/ to connect with our team now.
Comment on this and all of our posts on: LinkedIn, Twitter and Facebook.
Follow us to stay up to date on our industry insights and unique IT learning opportunities.

